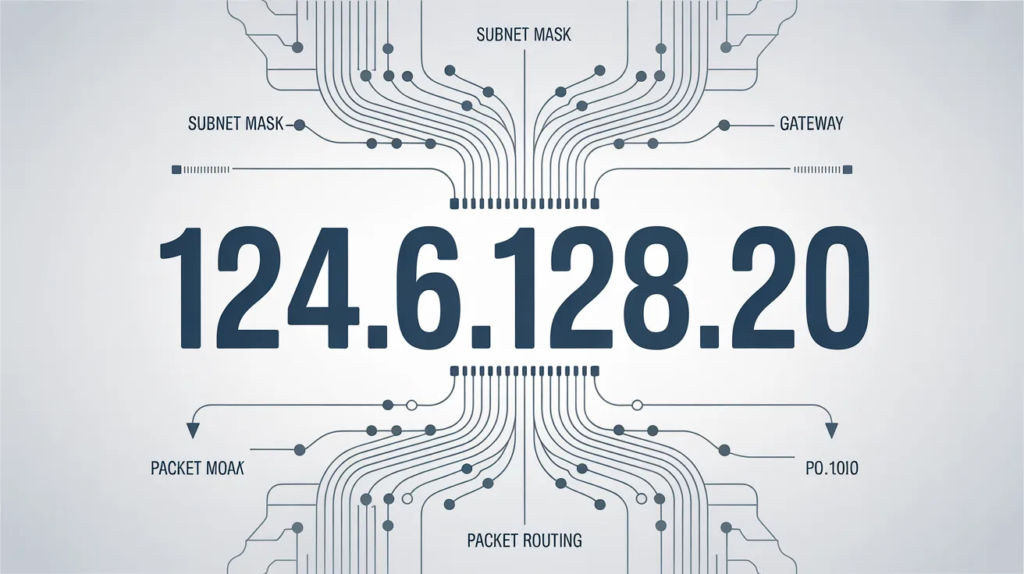
In the intricate web of digital connectivity, few elements are as fundamental yet overlooked as IP addresses. Take 124.6.128.20, for instance—a seemingly ordinary sequence that plays a pivotal role in how the internet operates. This IPv4 address, part of the vast system that routes data across the globe, exemplifies the backbone of modern networking. Whether you’re a tech professional troubleshooting connections or a curious user wondering about online privacy, grasping the nuances of 124.6.128.20 offers valuable insights into network architecture, security, and beyond. Let’s explore its structure, significance, and applications in detail, providing practical knowledge you can apply to your own digital experiences.
The Basics of IP Addresses: Breaking Down 124.6.128.20
Every device connected to the internet needs a unique identifier to send and receive information, and that’s where IP addresses come in. 124.6.128.20 follows the IPv4 format, which divides the address into four octets separated by dots. Each octet represents 8 bits, creating a 32-bit number that can support over four billion unique combinations—though we’re nearing exhaustion of available IPv4 addresses.
Analyzing 124.6.128.20 specifically, the first octet (124) indicates it’s in the Class A range, typically assigned to large networks. The subsequent numbers (6, 128, 20) refine its position within that block. This structure isn’t random; it’s governed by organizations like the Internet Assigned Numbers Authority (IANA) and regional registries. For 124.6.128.20, it falls under a subnet often used by telecom providers, ensuring efficient data flow without conflicts.
Understanding this breakdown adds value when diagnosing issues. For example, if you’re seeing 124.6.128.20 in your logs, knowing its class helps determine if it’s from a broad public network or a more localized one. This knowledge empowers better decision-making in firewall configurations or traffic analysis.
Ownership and Geolocation of 124.6.128.20
Ownership of IP addresses like 124.6.128.20 is allocated through regional internet registries, and in this case, it traces back to a major telecommunications company in Southeast Asia. Such assignments ensure that large-scale providers can manage vast pools of addresses for their customers, from mobile users to enterprise clients. 124.6.128.20 is part of a /24 subnet, meaning it’s one of 256 addresses in a contiguous block, often dedicated to specific services or regions.
Geolocation ties 124.6.128.20 to the Philippines, based on registry data and mapping tools. This doesn’t mean the device using it is physically there—IPs can be routed or proxied—but it provides a starting point for investigations. For businesses, this insight is crucial for compliance, such as adhering to data sovereignty laws or targeting regional content. If you’re running an e-commerce site, recognizing patterns from addresses like 124.6.128.20 could help tailor promotions to Asian markets, enhancing user engagement and conversion rates.
To illustrate geolocation accuracy, consider this table comparing typical IP mapping factors:
| Factor | Description | Impact on 124.6.128.20 |
|---|---|---|
| Registry Data | Official assignment from ARIN/APNIC | High reliability, points to Philippines telecom |
| Database Updates | Frequency of geolocation service refreshes | Moderate; can lag behind reassignments |
| User Mobility | Dynamic vs. static IP usage | Variable; mobile devices may shift locations |
| Proxy/VPN Influence | Masking true origin | Low for direct connections, but possible in secure setups |
| Accuracy Level | Overall precision | Country-level reliable, city-level approximate |
This table highlights why relying solely on geolocation for 124.6.128.20 requires cross-verification, adding practical value for security audits or marketing strategies.
The Role of 124.6.128.20 in Data Routing and Communication
Data doesn’t magically appear on your screen; it relies on addresses like 124.6.128.20 to navigate the complex paths of the internet. When you request a webpage, your device’s IP initiates the connection, and the server’s IP—potentially something like 124.6.128.20—responds by sending packets back. This process involves routers examining the address to forward data efficiently, minimizing latency.
In enterprise settings, 124.6.128.20 might represent a server handling email or web traffic. For instance, if it’s part of a content delivery network (CDN), it could cache popular files closer to users, speeding up load times. This efficiency is vital for high-traffic sites, where even milliseconds matter. By understanding how 124.6.128.20 fits into routing protocols like BGP (Border Gateway Protocol), network admins can optimize paths, reducing downtime and improving performance.
Real-world value comes from troubleshooting: If connections to 124.6.128.20 are slow, tools like traceroute can reveal hops along the way, pinpointing bottlenecks. This proactive approach saves time and resources, whether you’re managing a home network or a corporate infrastructure.
Security Implications Surrounding 124.6.128.20
No discussion of IP addresses is complete without addressing security, and 124.6.128.20 is no exception. As a public address, it’s exposed to the open internet, making it a potential target for scans or attacks. However, the address itself isn’t malicious—risk comes from how it’s used. For example, if 124.6.128.20 appears in your firewall logs with unusual patterns, it might indicate probing from a botnet.
To mitigate threats, implement IP whitelisting or blacklisting. If 124.6.128.20 is legitimate (e.g., from a trusted telecom), allow it; otherwise, block to prevent unauthorized access. Advanced techniques like intrusion detection systems (IDS) monitor traffic from addresses like 124.6.128.20, flagging anomalies such as sudden spikes in requests.
Privacy is another angle: Tools can trace 124.6.128.20 back to its provider, but not to individuals without legal processes. This underscores the importance of VPNs, which mask your IP and route through others, protecting your data. For users concerned about tracking, knowing about 124.6.128.20 encourages better habits, like using encrypted connections.
Here’s a security checklist table tailored to handling IPs like 124.6.128.20:
| Step | Action | Benefit |
|---|---|---|
| Monitor Logs | Regularly review access from 124.6.128.20 | Early detection of irregularities |
| Use Firewalls | Configure rules for public IPs | Blocks unwanted traffic |
| Employ Encryption | HTTPS/SSL for communications | Protects data in transit |
| Update Software | Patch systems vulnerable to IP-based exploits | Reduces attack surfaces |
| Educate Users | Train on IP awareness | Prevents phishing tied to spoofed addresses |
Applying this checklist provides immediate value, strengthening your network against common vulnerabilities.
Tracing and Analyzing 124.6.128.20: Tools and Techniques
Tracing an IP like 124.6.128.20 reveals its path and characteristics. Start with WHOIS queries, which disclose ownership and registration details. For 124.6.128.20, this confirms its telecom affiliation, offering context for any interactions.
Command-line tools like ping test responsiveness, while traceroute maps the route data takes to reach 124.6.128.20. Online platforms provide geolocation and reverse DNS lookups, showing if it’s associated with domains. These techniques are invaluable for IT pros diagnosing connectivity issues or investigating suspicious activity.
For deeper analysis, integrate with network monitoring software. If 124.6.128.20 shows up frequently, correlate it with events like login attempts to build a profile. This data-driven approach enhances troubleshooting, turning raw information into actionable intelligence.
Common Applications and Use Cases for 124.6.128.20
124.6.128.20 could serve various roles depending on its assignment. In telecom networks, it might handle mobile data routing, ensuring seamless browsing for users. Businesses use similar addresses for hosting services, where 124.6.128.20 could point to an email server or website backend.
In IoT ecosystems, IPs like 124.6.128.20 connect smart devices, enabling remote control. For developers, it’s a test bed for simulations, verifying how applications interact with real-world addresses. Understanding these uses helps in optimizing setups, whether scaling a server or securing a smart home.
Application breakdown table:
| Use Case | Description | Example with 124.6.128.20 |
|---|---|---|
| Web Hosting | Serving website content | Directing traffic to a regional site |
| Email Routing | Handling message delivery | Relaying emails in a telecom network |
| IoT Connectivity | Linking devices | Managing data from sensors in Philippines |
| Network Testing | Simulating connections | Debugging apps for Asian markets |
| VPN Endpoints | Secure tunneling | Routing encrypted traffic securely |
This table clarifies how 124.6.128.20 integrates into daily tech, offering strategies for implementation.
Challenges and Future Considerations for Addresses Like 124.6.128.20
IPv4 scarcity poses challenges for addresses like 124.6.128.20, driving the shift to IPv6 with its expansive pool. While 124.6.128.20 remains viable, compatibility issues arise in hybrid environments. Network admins must plan migrations to avoid disruptions.
Dynamic assignments mean 124.6.128.20 could change users, complicating tracking. Future trends include AI-driven management, automating optimizations for such IPs. Staying informed ensures you’re prepared for evolving standards.
Advanced Topics: Subnetting and Beyond with 124.6.128.20
Subnetting divides networks for efficiency, and 124.6.128.20 might be in a /24 mask, limiting it to 254 hosts. This setup aids in segmenting traffic, reducing congestion. For experts, calculating CIDR notations for 124.6.128.20 reveals its broadcast and network addresses, essential for configuration.
In cloud computing, IPs like 124.6.128.20 integrate with virtual private clouds, enhancing scalability. Mastering these concepts unlocks advanced networking, from designing resilient systems to implementing load balancing.
In conclusion, 124.6.128.20 exemplifies the quiet power of IP addresses in our connected world. From routing data to bolstering security, it underscores the importance of understanding digital foundations. By applying these insights, you can navigate networks more effectively, whether for personal use or professional endeavors.